Top videos
In this video I walkthrough the basics of the Ceaser Cipher and in the next video we will code it in Python.
Link to Python tutorial: https://www.youtube.com/watch?v=6YBqtYkzzmY&t=17s
🔥𝐄𝐝𝐮𝐫𝐞𝐤𝐚 𝐂𝐲𝐛𝐞𝐫 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐓𝐫𝐚𝐢𝐧𝐢𝐧𝐠 : https://www.edureka.co/cyberse....curity-certification 𝐂𝐨𝐝𝐞: 𝐘𝐎𝐔𝐓𝐔𝐁𝐄𝟐𝟎)
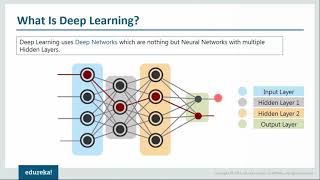
This Edureka video gives an introduction to Network Security and its nuances. It discusses the need of network security, tools for network security and various other fundamental concepts
🔴 Subscribe to our channel to get video updates. Hit the subscribe button above: https://goo.gl/6ohpTV
📝Feel free to share your list of top 10 trending technologies to learn in 2023 in the comments below.📝
🔴 𝐄𝐝𝐮𝐫𝐞𝐤𝐚 𝐎𝐧𝐥𝐢𝐧𝐞 𝐓𝐫𝐚𝐢𝐧𝐢𝐧𝐠 𝐚𝐧𝐝 𝐂𝐞𝐫𝐭𝐢𝐟𝐢𝐜𝐚𝐭𝐢𝐨𝐧𝐬
🔵 DevOps Online Training: http://bit.ly/3VkBRUT
🌕 AWS Online Training: http://bit.ly/3ADYwDY
🔵 React Online Training: http://bit.ly/3Vc4yDw
🌕 Tableau Online Training: http://bit.ly/3guTe6J
🔵 Power BI Online Training: http://bit.ly/3VntjMY
🌕 Selenium Online Training: http://bit.ly/3EVDtis
🔵 PMP Online Training: http://bit.ly/3XugO44
🌕 Salesforce Online Training: http://bit.ly/3OsAXDH
🔵 Cybersecurity Online Training: http://bit.ly/3tXgw8t
🌕 Java Online Training: http://bit.ly/3tRxghg
🔵 Big Data Online Training: http://bit.ly/3EvUqP5
🌕 RPA Online Training: http://bit.ly/3GFHKYB
🔵 Python Online Training: http://bit.ly/3Oubt8M
🌕 Azure Online Training: http://bit.ly/3i4P85F
🔵 GCP Online Training: http://bit.ly/3VkCzS3
🌕 Microservices Online Training: http://bit.ly/3gxYqqv
🔵 Data Science Online Training: http://bit.ly/3V3nLrc
🌕 CEHv12 Online Training: http://bit.ly/3Vhq8Hj
🔵 Angular Online Training: http://bit.ly/3EYcCTe
🔴 𝐄𝐝𝐮𝐫𝐞𝐤𝐚 𝐑𝐨𝐥𝐞-𝐁𝐚𝐬𝐞𝐝 𝐂𝐨𝐮𝐫𝐬𝐞𝐬
🔵 DevOps Engineer Masters Program: http://bit.ly/3Oud9PC
🌕 Cloud Architect Masters Program: http://bit.ly/3OvueZy
🔵 Data Scientist Masters Program: http://bit.ly/3tUAOiT
🌕 Big Data Architect Masters Program: http://bit.ly/3tTWT0V
🔵 Machine Learning Engineer Masters Program: http://bit.ly/3AEq4c4
🌕 Business Intelligence Masters Program: http://bit.ly/3UZPqJz
🔵 Python Developer Masters Program: http://bit.ly/3EV6kDv
🌕 RPA Developer Masters Program: http://bit.ly/3OteYfP
🔵 Web Development Masters Program: http://bit.ly/3U9R5va
🌕 Computer Science Bootcamp Program : http://bit.ly/3UZxPBy
🔵 Cyber Security Masters Program: http://bit.ly/3U25rNR
🌕 Full Stack Developer Masters Program : http://bit.ly/3tWCE2S
🔵 Automation Testing Engineer Masters Program : http://bit.ly/3AGXg2J
🌕 Python Developer Masters Program : https://bit.ly/3EV6kDv
🔵 Azure Cloud Engineer Masters Program: http://bit.ly/3AEBHzH
🔴𝐄𝐝𝐮𝐫𝐞𝐤𝐚 𝐔𝐧𝐢𝐯𝐞𝐫𝐬𝐢𝐭𝐲 𝐏𝐫𝐨𝐠𝐫𝐚𝐦𝐬
🌕 Professional Certificate Program in DevOps with Purdue University: https://bit.ly/3Ov52lT
🔵 Advanced Certificate Program in Data Science with E&ICT Academy, IIT Guwahati: http://bit.ly/3V7ffrh
🌕 Artificial and Machine Learning PGD with E&ICT Academy
NIT Warangal: http://bit.ly/3OuZ3xs
📢📢 𝐓𝐨𝐩 𝟏𝟎 𝐓𝐫𝐞𝐧𝐝𝐢𝐧𝐠 𝐓𝐞𝐜𝐡𝐧𝐨𝐥𝐨𝐠𝐢𝐞𝐬 𝐭𝐨 𝐋𝐞𝐚𝐫𝐧 𝐢𝐧 2023 𝐒𝐞𝐫𝐢𝐞𝐬 📢📢
⏩ NEW Top 10 Technologies To Learn In 2023 - https://youtu.be/udD_GQVDt5g
📌𝐓𝐞𝐥𝐞𝐠𝐫𝐚𝐦: https://t.me/edurekaupdates
📌𝐓𝐰𝐢𝐭𝐭𝐞𝐫: https://twitter.com/edurekain
📌𝐋𝐢𝐧𝐤𝐞𝐝𝐈𝐧: https://www.linkedin.com/company/edureka
📌𝐈𝐧𝐬𝐭𝐚𝐠𝐫𝐚𝐦: https://www.instagram.com/edureka_learning/
📌𝐅𝐚𝐜𝐞𝐛𝐨𝐨𝐤: https://www.facebook.com/edurekaIN/
📌𝐒𝐥𝐢𝐝𝐞𝐒𝐡𝐚𝐫𝐞: https://www.slideshare.net/EdurekaIN
📌𝐂𝐚𝐬𝐭𝐛𝐨𝐱: https://castbox.fm/networks/505?country=IN
📌𝐌𝐞𝐞𝐭𝐮𝐩: https://www.meetup.com/edureka/
📌𝐂𝐨𝐦𝐦𝐮𝐧𝐢𝐭𝐲: https://www.edureka.co/community/
Is there any eligibility criteria for this program?
A potential candidate must have one of the following prerequisites: Degrees like BCA, MCA, and B.Tech or Programming experience Should have studied PCM in 10+2
About the course
About Cyber security Certification Course
Cybersecurity is the combination of processes, practices, and technologies designed to protect networks, computers, programs, data and information from attack, damage, or unauthorized access. In this best Cyber security training Course, you will learn about the aspects of Cyber security from defensive as well as offensive side, along with the methodologies that must be practiced, ensuring information security of an organization.